|
 |
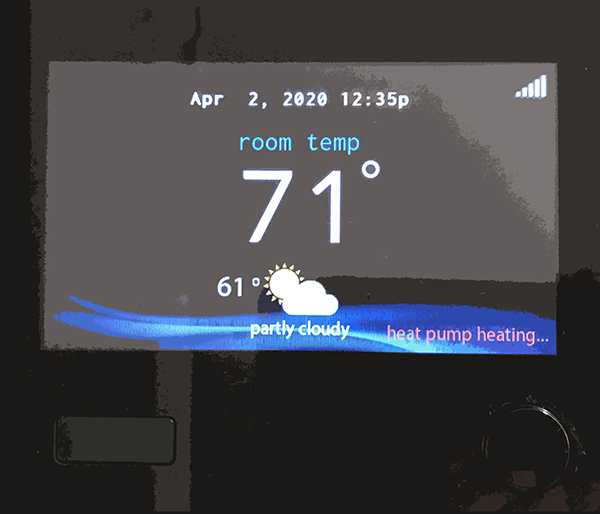
This internet-connected 'smart thermostat' is one of many IoT devices being used in homes today. |
|
The demand for internet-connected “smart home” and small business Internet of Things (IoT) devices is growing rapidly, but so too are concerns regarding how easily their hardware and software can be compromised. Recent news stories about smart speakers and surveillance cameras being hijacked by hackers has raised public awareness of their potential misuse.
Securing a network is a complex task made even more challenging when IoT devices are connected to it. A new draft white paper from the National Institute of Standards and Technology’s National Cybersecurity Center of Excellence (NCCoE) describes an approach to determining and documenting the device types and communication behaviors of IoT devices connected to a network.
"Methodology for Characterizing Network Behavior of Internet of Things Devices" currently is available for public comment. It was written by Paul Watrobski and Joshua Klosterman of the MITRE Corporation, McLean, Va.; William Barker of Dakota Consulting in Gaithersburg, Md; and Murugiah Souppaya in the Information Technology Laboratory of NIST’s Computer Security Division.
Watrobski is a Ph.D. student in Reliability Engineering and an M.S. student in Electrical and Computer Engineering. He is co-advised by Distinguished University Professor John Baras (ECE/ISR) and Associate Professor Michel Cukier (ME).
The paper demonstrates how manufacturers and network administrators could use device characterization techniques to describe IoT device communication requirements in support of the NIST National Cybersecurity Center of Excellence’s (NCCoE) Mitigating IoT-Based DDoS project—specifically, how to capture IoT device network communications to generate and analyze Manufacturer Usage Description (MUD) files.
Such efforts will lead to more accurate management of network access to and from IoT devices, and help ensure that the devices perform as the device manufacturers and device owners intend. The paper also describes the current state of implementation of the approach and proposals for future development.
Project status and resources
You can read about the status of the project on the NIST NCCoE page, "Securing IoT Devices using MUD." There also is a page of MUD-related resources, and a public github page for the tool Watrobski developed that is described in the paper.
Obtaining a PDF of the paper
The PDF of the paper is located here on the NIST website. Comments are due by May 1, 2020 and should be emailed to mitigating-iot-ddos-nccoe@nist.gov
Related Articles:
New graduate program in Embedded Systems
FCC Commissioner Geoffrey Starks visits UMD 5G Secure Test Bed
FCC Commissioner Nathan Simington visits UMD 5G Secure Test Bed
Fatemeh Alimardani receives WTS-DC scholarship
ISR faculty leading, playing key roles in ARL cooperative agreement
Improving patient health, one Amazon Alexa at a time
Gang Qu elected IEEE Fellow
Wu and Wong granted U.S. patent for method to detect counterfeiting
Real-time remote reconstruction of signals for the Internet of Things
John Baras named Fellow of American Institute of Aeronautics and Astronautics
April 2, 2020
|

